MAC Filtering (or layer 2 address filtering): MAC filtering refers to a security access control method whereby the 48-bit address (also called MAC address) assigned to each network card is used to determine access to the network. MAC addresses are uniquely assigned to each card, so using MAC filtering on a network permits and denies network access to specific devices through the use of blacklists and whitelists. To limit the number of computers to a known few, configuring MAC filtering is a very good option. This is configured on the wireless router and not on the client computers. Any wireless network, SSID needs to be configured on the wireless router. Note that if the router broadcasts SSID, then the clients will automatically learn about the wireless network. If the SSID broadcast is disabled on the router, you need to configure the clients with proper SSID (same as that of the router SSID).
Enable MAC Filtering: MAC limiting the MAC addresses that can access the wireless network, you can prevent unauthorized computers from accessing your wireless network. Note that each MAC address is unique, and hence MAC address filtering can effectively prevent unauthorized computer access. By using MAC filtering, you can allow or disallow certain MAC addresses only. Note that even if the SSID broadcast is turned off, it is possible to access the wireless network if the intruder some how knows the network name.
Changing default SSID: SSID, short for service set identifier, a unique identifier attached to the header of packets sent over a WLAN. The SSID differentiates one WLAN from another, so all access points and all devices attempting to connect to a specific WLAN must use the same SSID. You can hide the SSID so that it is not broadcast over the wireless network. For encryption, enable WPA2 (or the older versions like WPA). This would provide basic protection for the wireless network. Remember to use difficult to guess password for WPA2.
Installing an authentication server or an external Firewall incurs additional costs, and not a best solution. By default, SSID is broadcast by a wireless access point. By disabling SSID broadcast, the wireless network existence may be hidden. However, if SSID broadcast is disabled, one needs to pre-configure the SSID on a client workstation manually. Otherwise, it wouldn't be possible to communicate in the wireless network. Enabling SSID broadcast will only announce the network to neighborhood devices, thus lessening the security of the network.
Wi-Fi Protected Access (WPA) and Wi-Fi Protected Access II (WPA2) are two security protocols and security certification programs developed by the Wi-Fi Alliance to secure wireless computer networks. It is possible that several networks are operating at the same frequencies. It is recommended that you change the WI-FI channel and see if it solves the problem.
WPA: WPA, short for Wi-Fi Protected Access, is a Wi-Fi standard that was designed to improve upon the security features of WEP (Wired Equivalent Privacy). The technology is designed to work with existing Wi-Fi products that have been enabled with WEP.
WPA2: WPA2 is an encryption standard, and client workstations will still be able to see SSID even if the WPA2 and Mac filtering are enabled. MAC filtering is another security precaution, which enables (or disables) listed MAC addresses in the internal MAC filter table of WAP. You need to manually enter the MAC addresses for this purpose. SSID needs to be configured on the laptop for connecting to the Access Point. The DHCP server typically supplies IP address, DNS server information, and subnet mask. To secure the wireless router for home use from unauthorized access you need to change the default login/password on a router soon after the router is installed. Secondly, ensure to set encryption such as WPA2 so that only authorized users will be able to access the wireless network.

Note that for WPA encryption, you need to configure it on the wireless router and on all the workstations. To enable MAC filtering, you need to gather the MAC addresses of all client computers, and feed it into the wireless router
The specifications for various 802.11 standards is as given in table 1:
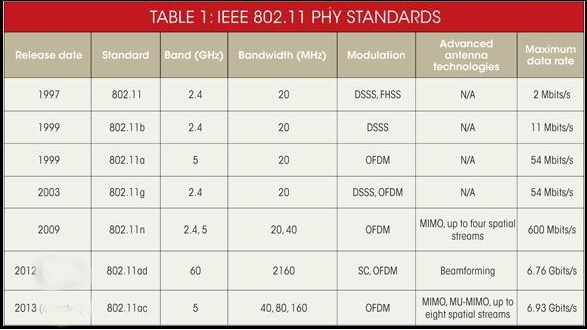
As can be seen in the table, 802.11ac works at 5 GHz, and supports bandwidth up to 6.93Gbits/sec.

Note: MIMO (multiple input, multiple output) is an antenna technology for wireless communications in which multiple antennas are used at both the source (transmitter) and the destination (receiver). The antennas at each end of the communications circuit are combined to minimize errors and optimize data speed. MIMO is one of several forms of smart antenna technology, the others being MISO (multiple input, single output) and SIMO (single input, multiple output).
Parental Control: The parental controls built into Windows 7/8/10 help parents determine which games their children can play, which programs they can use, and which websites they can visit, and when. Parents can restrict computer use to specific times and trust that Windows OS will enforce those restrictions, even when they're away from home.
Content filtering: To set the content filtering on the Android phone , go to apps > menu key. Choose 'Settings' and then “Parental Controls” then choose appropriately from 'Set Content Restrictions'. You can now choose which apps are allowed on your phone.
Port Forwarding: The computers on the network have been configured to use DHCP and private IP addresses. Therefore, you need to set up port forwarding to access the host computer running RDP. Remember, RDP uses port 3389 by default.
Locking Android phone: Locking your Android smartphone with a password, PIN or unlock pattern is your first defense against those who would use it for malicious purposes like stealing your info or sending joke texts to your friends and family. To setup, go to Settings/Security/ Set up screen lock, and choose to enter a pattern, or a password or a PIN. If you are looking for fast and easy way to unlock your smart phone, choose "Pattern".
Common wireless security protocols
Features of RADIUS server:
1. Open standard, and widely supported. Note that TACACS+ is a Cisco proprietary standard, but well supported too.
2. Use UDP port
3. Provides extensive accounting capability when compared with TACACS+ server
4. Only the password is encrypted in packets transiting between the RADIUS server and the client (any device acting as client, such as a router or a switch or a host computer).
5. There is a new upgrade expected, named Diameter.
Features of TACACS+ server
Granular control: TACACS+ uses the AAA (AAA refers to Authentication, Authorization and Accounting) architecture, which separates AAA. This allows separate solutions that can still use TACACS+ for be used for authentication, authorization and accounting. For example, with TACACS+, it is possible to use Kerberos authentication and TACACS+ authorization and accounting. TACACS+ is very commonly used for device administration.
TACACS+ encrypts the entire body of the packet but leaves a standard TACACS+ header.
TACACS+ is a Cisco proprietary protocol (later became an Open standard), and very widely supported by various vendors offering AAA servers. Note that RADIUS is an Open Standard and widely supported too.
TACACS+ uses TCP port (port #49) to communicate between the server and the client.
TACACS+ provides complete encryption for communication between the TACACS+ server and the client.