RETIRED! Exam
Firewalls configured in transparent mode are also sometimes referred to as bridging, layer-2 or stealth firewalls since they operate at layer 2 of the OSI reference model. A transparent firewall can use packet based filtering, stateful filtering, application inspection. Usually, Transparent firewall is applied where it is not possible to apply other types of firewall due to reasons like separation of duties etc. Some corporations may also find benefits in deploying a transparent firewall in their wireless segments.
IronPort Email Security Appliances: Provides granular control of email providing thorough security against email services
IronPort Web Security Appliances (WSA): Provides granular control of web traffic by tracking thousands of applications and enforce security policies to protect networks against threats.
ASA Firewall: ASA stands for Adaptive Security Appliance. In brief, Cisco ASA is a security device that combines firewall, antivirus, intrusion prevention, and virtual private network (VPN) capabilities. It provides proactive threat defence that stops attacks before they spread through the network. Cisco 5500 series devices are examples of Cisco ASA capable devices.
Integrated Services Router (ISR): As the name implies, ISR routers provide integrated services such as VOIP, Video, and firewall functionality. ISR routers are primarily intended for branch office use.
IPS: Short for Intrusion Prevention System, a device enabled with IPS scans network activity, and logs for any malicious activity, and blocks it before it does any damage to the network. IPS may be considered as an extension to IDS (Intrusion Detection System). The difference being that IPS detects intrusions before they really occur.
ScanSafe: Cisco ScanSafe is a cloud hosted web filtering service which enables you to create, enforce and monitor Web usage policies. Layering real time rule-based filters with up-to-date and accurate categorization database. Web Filtering enforces your organization's acceptable usage policy, protecting you from the legal liabilities of inappropriate content, reducing bandwidth congestion and improving employee productivity.
Cisco SecureX architecture enforces security policies across the entire distributed network, not just at a single point in the data stream. Cisco SecureX:
Cisco's SecureX architecture has the following elements:
1. Context awareness: May be used to confirm parameters like user authentication, access control, etc. Actual tools to implement this include ISE, NAC, and AAA.
2. AnyConnect Client: With AnyConnect Client, you can establish Secure Sockets Layer (SSL) or IPsec VPNs for clients.
3. TrustSec: This creates a distributed access policy enforcement mechanism, and can also provide confidentiality using encryption. It is used to control end-to-end security, based on who are connected to the network, and analyse whether the end systems are secure or not. Actual tools to implement this include ISE, NAC, and AAA.
4. Security Intelligence Operations: Security Intelligence Operations (SIO) is a cloud-based service that Cisco manages. This service identifies and correlates real-time threats so that the network resources may be secured using real time information. A prior knowledge of network threats enables network administrators to take appropriate preventive action.

1. The ASA supports both standard and extended access lists.
2. ASA doesn't use a wildcard mask. Instead, it uses netmask in the access control list (ACL) for permit, deny statements.
Graphical tools used with ASA firewall:
You can use several tools to manage an ASA, including the following:
Note that CCP (Cisco Configuration Professional) does not support ASA.
Cisco ASA Interface security levels
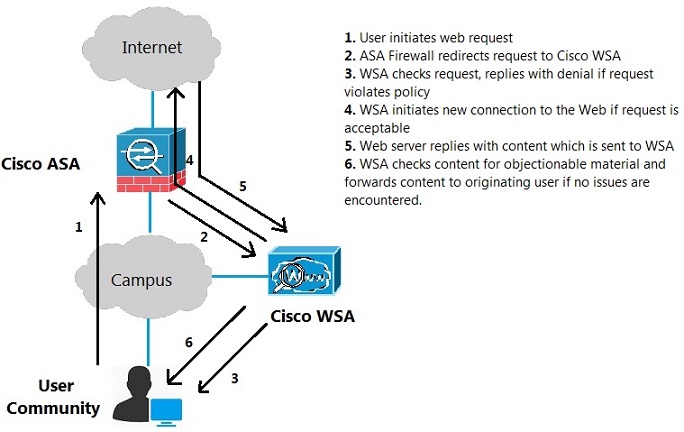
The figure shows WSA connected in transparent proxy mode, that the user won't be seeing it. The sequence of operations involved in fulfilling a request from Internet user inside the community is shown.