Connection oriented Protocols:
1. It guarantees transmitted data will reach its destination
2. It sequences the packets such that the packets are received in a sequenced manner at the destination.
3. TCP/IP is an example of connection oriented protocol.
Connectionless protocols:
1. Connectionless protocols do not guarantee packet delivery.
2. The advantage is less over-head.
3. UDP/IP is an example of connectionless protocol.
TCP/IP is a suite of data communications protocols. Two of the more important protocols in the suite are the TCP and the IP. The full form of TCP/IP is Transmission Control Protocol/Internet Protocol. A suite of protocols for communication between computers and specifying standards for transmitting data over networks.
IP provides the basic packet delivery service for all TCP/IP networks. IP is a connectionless protocol, which means that it does not exchange control information to establish an end-to-end connection before transmitting data. A connection-oriented protocol exchanges control information with the remote computer to verify that it is ready to receive data before sending it.
IP relies on protocols in other layers to establish the connection if connection-oriented services are required and to provide error detection and error recovery. IP is sometimes called an unreliable protocol, because it contains no error detection or recovery code.
TCP is a connection oriented protocol whereas UDP is connectionless protocol. TCP uses sequence numbers for tracking the receipt of the packets at the destination. UDP is more like a telegram, and any packets that does not arrive at the destination can not be determined. This function has to be done by the application layer (or higher level protocols). Hence, it (UDP) is also known as connectionless protocol. A detailed comparison of both TCP and UDP protocols is given below.
Two types of Internet Protocol (IP) are Transmission Control Protocol (TCP) and User Datagram Protocol (UDP). TCP is connection oriented and data can be sent bidirectional after establishment of a connection. UDP is a simpler, connectionless Internet protocol. Multiple messages are sent as packets in chunks using UDP.
| Suitability | TCP is suited for applications that require high reliability, and not very critical of transmission delays. | UDP is suitable for applications that need fast, efficient transmission, such as games. UDP's stateless nature is also useful for servers that answer small queries from a large numbers of clients. |
| Use by protocols | HTTP, HTTPs, FTP, SMTP, Telnet | DNS, DHCP, TFTP, SNMP, RIP, VOIP. |
| Ordering of data packets | TCP rearranges data packets in the order specified. | UDP has no inherent order as all packets are independent of each other. If ordering is required, it has to be managed by the application layer. |
| Speed and reliability | The speed for TCP is slower than UDP. When using TCP, any missing packets are retransmitted. TCP guarantees packet delivery and hence more reliable. | UDP is faster because error recovery is not attempted. It is a "best effort" protocol. There is no guarantee that a packet is received at the destination and hence less reliable than TCP. |
| Header Size | TCP header size is 20 bytes | UDP Header size is 8 bytes. |
| Common Header Fields | Source port, Destination port, Check Sum | Source port, Destination port, Check Sum |
| Streaming of data | Data is read as a byte stream, no distinguishing indications are transmitted to signal message (segment) boundaries. | Packets are sent individually and are checked for integrity only if they arrive. Packets have definite boundaries which are honored upon receipt, meaning a read operation at the receiver socket will yield an entire message as it was originally sent. |
| Connection Setup | TCP requires three packets to set up a socket connection, before any user data can be sent. | UDP is lightweight. There is no ordering of messages, no tracking connections, etc. It is a small transport layer designed on top of IP. |
| Data Flow Control | TCP does Flow Control. TCP requires three packets to set up a socket connection, before any user data can be sent. TCP handles reliability and congestion control. | UDP does not have an option for flow control |
| Error Checking | TCP does error checking and error recovery. Erroneous packets are retransmitted from the source to the destination. | UDP does error checking but simply discards erroneous packets. Error recovery is not attempted. |
| Fields | 1. Sequence Number, 2. AcK number, 3. Data offset, 4. Reserved, 5. Control bit, 6. Window, 7. Urgent Pointer 8. Options, 9. Padding, 10. Check Sum, 11. Source port, 12. Destination port | 1. Length, 2. Source port, 3. Destination port, 4. Check Sum |
| Acknowledgement | Acknowledgement segments | No Acknowledgment |
| Handshake | SYN, SYN-ACK, ACK | No handshake (connectionless protocol) |

UDP is sometimes referred to as "send and pray" because there is no reliable delivery mechanism inherent in UDP. TCP is known as a reliable protocol.
IP Packets: A packet is a block of data that carries with it the information necessary to deliver it to a destination address. A packet-switching network uses the addressing information in the packets to switch packets from one physical network to another, moving them toward their final destination. Each packet travels the network independently of any other packet. The datagram is the packet format defined by IP.
IP Functions: Some of the functions IP performs include:
Moving Data Between the Network Access Layer and the Host-to-Host Transport Layer : When IP receives a datagram that is addressed to the local host, it must pass the data portion of the datagram to the correct host-to-host transport layer protocol. IP uses the protocol number in the datagram header to select the transport layer protocol. Each host-to-host transport layer protocol has a unique protocol number that identifies it to IP.
Routing Datagrams to Remote Hosts: Internet gateways are commonly referred to as IP routers because they use IP to route packets between networks. In traditional TCP/IP terms, there are only two types of network devices: gateways and hosts. Gateways forward packets between networks, and hosts do not. However, if a host is connected to more than one network (called a multi-homed host), it can forward packets between the networks. When a multi-homed host forwards packets, it acts like any other gateway and is considered to be a gateway.
Fragmenting and Reassembling Datagrams: As a datagram is routed through different networks, it may be necessary for the IP module in a gateway to divide the datagram into smaller pieces. A datagram received from one network may be too large to be transmitted in a single packet on a different network. This condition occurs only when a gateway interconnects dissimilar physical networks.
Each type of network has a maximum transmission unit (MTU) that determines the largest packet it can transfer. If the datagram received from one network is longer than the other network's MTU, it is necessary to divide the datagram into smaller fragments for transmission in a process called fragmentation.
IP Layering: TCP/IP is organized into four conceptual layers (as shown in Figure 1). Below fig shows TCP/IP Conceptual Layers
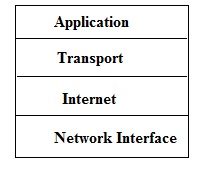
TCP/IP Conceptual Layers
Network Interface Layer: The network interface layer is the lowest level of the TCP/IP protocol stack. It is responsible for transmitting datagrams over the physical medium to their final destinations.
Internet Layer: The Internet layer is the second level of the TCP/IP protocol stack. It provides host-to-host communication. In this layer, packets are encapsulated into datagrams, routing algorithms are run, and the datagram is passed to the network interface layer for transmission on the attached network.
Transport Layer: The transport layer is the third level of the TCP/IP protocol stack. It is responsible for providing communication between applications residing in different hosts. By placing identifying information in the datagram (such as socket information), the transport layer enables process-to-process communication. The transport layer provides either a reliable transport service (TCP) or an unreliable service (User Data Protocol). In a reliable delivery service, the destination station acknowledges the receipt of a datagram.
Application Layer: The application layer is the fourth and highest level of the TCP/IP protocol stack. Some applications that run in this layer are: Telnet,FTP,SMTP,Simple Network Management Protocol (SNMP),Domain Name System (DNS)

Transmission Control Protocol(TCP) and User Datagram Protocol (UDP) operate at the Transport Layer. IP operates at Network Layer whereas FTP operates at the Application Layer