RETIRED!
Subnet Masking:Like IP addresses, a subnet mask contains four bytes (32 bits) and is often written using the same "dotted-decimal" notation.
A subnet mask is different from an IP address, and it doesn't exist independently from the IP address. Instead, subnet masks accompany an IP address and the two values work together. Applying the subnet mask to an IP address splits the address into two parts, an "extended network address" and a host address. If we don't specify a subnet along with an IP address, usually the default subnet mask is assumed.
The default subnet masks for various classes of IP addresses are given below:
Class A: 255.0.0.0
Class B: 255.255.0.0
Class C: 255.255.255.0
The IP address and default gateway on a computer should be in the same network (or subnet). By following this rule one of the two given addresses (200.122.21.1 or 200.122.21.255) is a default gateway. However, the address 200.122.21.255 is a broadcast address and could not qualify for a default gateway. That leaves us with only one option.
An IP address is considered private if the IP number falls within one of the IP address ranges reserved for private uses by Internet standards groups. These private IP address ranges exist:
10.0.0.0 through 10.255.255.255
172.16.0.0 through 172.31.255.255
192.168.0.0 through 192.168.255.255
Private IP addresses are typically used on local networks including home, school and business LANs including airports and hotels.
The IP address FC00::42A:0:0:7F5 is an IPv6 address with leading zeros omitted and using zero compression.
For accessing the Internet using static IP addressing, you need to configure the IP address, subnet mask, default gateway (if required by the ISP), and DNS server information.
APIPA stands for Automatic Private IP Addressing. A feature of Microsoft Windows, APIPA is a DHCP failover mechanism. With APIPA, DHCP clients can obtain IP addresses when DHCP servers are nonfunctional. APIPA exists in all popular versions of Windows except Windows NT.
IPv4 vs IPv6: An IP address is binary numbers but can be stored as text for human readers. For example, a 32-bit numeric address (IPv4) is written in decimal as four numbers separated by periods. Each number can be zero to 255. For example, 1.160.10.240 could be an IP address.
IPv6 addresses are 128-bit IP address written in hexadecimal and separated by colons. An example IPv6 address could be written like this: 3ffe:1900:4545:3:200:f8ff:fe21:67cf.
TCP and UDP ports, protocols and their purpose. Some important port numbers are as given below
21 - FTP (File Transfer Protocol)
22 - SSH (Secure Shell)
23 - TELNET
25 - SMTP (Simple Mail Transfer Protocol)
53 - DNS (Domain Name System)
80 - HTTP (Hypertext Transfer Protocol)/WWW
110 - POP3 (Post Office Protocol version 3)
143 - IMAP (Internet Message Access Protocol
443 - HTTPS (Hyper Text Transfer Protocol Secure)
3389 - RDP (Remote Desktop Protocol)
137-139 NetBIOS/NetBT
445 - SMB/CIFS (Server Message Block /Common Internet File System)
427 - SLP (Service Location Protocol)
548 - AFP (Apple Filing Protocol)
Hyper Text Transfer Protocol Secure (HTTPS) is the secure version of HTTP, the protocol over which data is sent between your browser and the website that you are connected to. The 'S' at the end of HTTPS stands for 'Secure'. It means all communications between your browser and the website are encrypted. HTTPS is often used to protect highly confidential online transactions like online banking and online shopping order forms.
Web browsers such as Internet Explorer, Firefox and Chrome also display a padlock icon in the address bar to visually indicate that a HTTPS connection is in effect.
SMTP stands for Simple Mail Transfer Protocol. SMTP is used when email is delivered from an email client, such as Outlook Express, to an email server or when email is delivered from one email server to another. SMTP uses port 25.SMTP is used to upload mail to the mail server.
POP3 stands for Post Office Protocol. POP3 allows an email client to download an email from an email server. The POP3 protocol is simple and does not offer many features except for download. Its design assumes that the email client downloads all available email from the server, deletes them from the server and then disconnects. POP3 normally uses port 110.POP3 is used for downloading mail from a mail server to a client machine running POP3 client. SMTP can be used to upload mail over Internet to a Mail server. Note that POP3 is used to read email.
IMAP stands for Internet Message Access Protocol. IMAP shares many similar features with POP3. It, too, is a protocol that an email client can use to download email from an email server. However, IMAP includes many more features than POP3. The IMAP protocol is designed to let users keep their email on the server. IMAP requires more disk space on the server and more CPU resources than POP3, as all emails are stored on the server. IMAP normally uses port 143.
The Domain Name System (DNS) translates Internet domain and host names to IP addresses.On the Internet, DNS automatically converts between the names we type in our Web browser address bar to the IP addresses of Web servers hosting those sites. Larger corporations also use DNS to manage their own company intranet. Home networks use DNS when accessing the Internet
FTP (File Transfer Protocol) is used for uploading and downloading files from a server. You can use FTP to access your files which are hosted on your company server or Internet. Uses port 21. Filezilla is a well known FTP client software. Note that the server must be running FTP server daemon to transfer files to a client computer. It is used in a client/server configuration to transfer files. It can operate in active or passive mode and uses TCP to control the connection. In active mode, the connection is initiated by the client. It informs the server about which port it intends to use to receive data. In active mode (although port 21 is used for command and control) the data will be sent out on port 20 which serves as the FTP servers data port.
Usually, a sector contains 512 bytes. To find out the size of a hard disk, use the formula: (# of cylinders X # of sectors X # of heads) X 0.5 KB
FTP is a client-server protocol that is used for transfering files between a client and a remote host computer on a TCP/IP network. FTP (File Transfer Protocol) is used for uploading and downloading files from a server. You can use FTP to access your files which are hosted on your company server or Internet. Uses port 21. Filezilla is a well known FTP client software. Note that the server must be running FTP server daemon to transfer files to a client computer.
Telnet is a protocol that allows you to connect to remote computers (called hosts) over a TCP/IP network (such as the Internet). Using telnet client software on your computer, you can make a connection to a telnet server (i.e., the remote host). Once your telnet client establishes a connection to the remote host, your client becomes a virtual terminal, allowing you to communicate with the remote host from your computer. Usually, telnet requires you to login to the remote system, which means that your system administrator had configured your login username and password on the remote host already.
Router: A router for Internet sharing is normally configured using web browser. High-end routers may provide option for terminal connectivity, where in you can connect a terminal, and issue commands for configuring the router.
MAC filtering (Media Access Control) :Filtering refers to a security access control method where an address is assigned to each network card that's used to determine access to the network.
DHCP (Dynamic Host Configuration Protocol) :A network protocol that enables a server to automatically assign an IP address to a computer from a defined range of numbers
SMTP : The Simple Mail Transport Protocol (SMTP) uses TCP port 25 for internet mail transmission. It is an internet standard protocol.
AFP : The Apple File Protocol (AFP) version 3.0 and higher use TCP/IP ports 548 or 427 to support the proprietary Apple sharing protocol.
Secure Shell (SSH): is a cryptographic remote login protocol for secure data communication over an unsecured network. Designed as a replacement for telnet and rlogin, which send information in plaintext, SSH client and server programs provide strong host-to-host and user authentication as well as a number of securely encrypted methods of communication to provide confidentiality and integrity of data. SSH supports data stream compression between the client and the server.
TheLightweight Directory Access Protocol (LDAP)is a directory service protocol that runs on a layer above the TCP/IP stack. It provides a mechanism used to connect to, search, and modify Internet directories. The LDAP directory service is based on a client-server model. The function of LDAP is to enable access to an existing directory.
SMB: he Server Message Block Protocol is a client-server communication protocol used for sharing access to files, printers, serial ports and other resources on a network. SMB is the native Windows network file sharing protocol is the preferred protocol for Windows clients.
AFP: The Apple Filing Protocol formerly AppleTalk Filing Protocol, is a proprietary network protocol that offers file services for Mac OS X and original Mac OS. AFP is the protocol for all Mac clients through OS X 10.8, SMB is the standard for Windows clients, and NFS is perfect between UNIX servers. With the release of OS X 10.9 "Mavericks", Apple fully supports both SMB2 and AFP. AFP is the native file and printer sharing protocol for Macs and it supports many unique Mac attributes that are not supported by other protocols.
Performance and reliability
Remote Desktop in Windows 7 Professional uses Remote Desktop Protocol (RDP), which in turn uses port 3389. Therefore, you need to configure port forwarding on Port 3389 to access remote desktop. The port forwarding is usually configured on the router that communicates with the external network (Internet). Remote Desktop Protocol (RDP) is a proprietary protocol developed by Microsoft, which provides a user with a graphical interface to connect to another computer over a network connection. The user employs RDP client software for this purpose, while the other computer must run RDP server software.
RDP servers are built into Windows operating systems; an RDP server for Linux and OSX also exists. By default, the server listens on TCP port 3389.
NFS is good for UNIX server-to-server file sharing. However it is incompatible with Windows clients.
Network Types:
A LAN (local area network) is a group of computers and network devices connected together, usually within the same building. By definition, the connections must be high speed and relatively inexpensive (e.g., token ring or Ethernet). A LAN connection is a high-speed connection to a LAN. For example, most of the buildings within a campus are connected using a LAN.
A MAN (metropolitan area network) is a larger network that usually spans several buildings in the same city or town. For example, if your organization has several buildings spread across the city, then they may be connected via MAN.
A WAN (wide area network), in comparison to a MAN, is not restricted to a geographical location, although it might be confined within the bounds of a state or country. A WAN connects several LANs, and may be limited to an enterprise (a corporation or an organization) or accessible to the public. The technology is high speed and relatively expensive. The Internet is an example of a worldwide public WAN.
PAN: PAN stands for Personal Area Network. It is a network which connects devices within small range typically on the order of 10 to 100 meters. Device in one PAN network can establish connection with another device in other PAN network when in the range. All the short range wireless technologies fall under PAN viz. Bluetooth, Zigbee, Zwave, Infrared etc. It is mainly designed and developed for low data rate monitoring and control applications. PAN wireless technologies have become very popular in IoT (Internet of things) networks.
Following are the characteristics of PAN:
Note that LAN technologies typically use Ethernet technologies where as PAN technologies use Bluetooth, Zigbee, etc. Dial-up Internet and DSL use copper wire for connecting to the Internet. In the case of DSL, there is a distance limitation between the Hub and the customer premises, beyond which the DSL may not work. Cable Internet uses co-axial cable that connects to your cable TV. Satellite Internet uses a satellite dish, and usually initial costs are more expensive. Satellite Internet is commonly used when broadband connectivity is required at remote locations that do not have traditional cable or DSL Internet. A DSL modem most commonly uses normal telephone line (Twisted Pair or TP) for connecting to the Internet. Dial-up offers the lowest speed among the other Internet access schemes. Cable Internet uses co-axial cable and a cable modem to connect to the Internet and offers highest download speeds up to a maximum of 3 Mbps (theoretically, download speeds are much higher than this). This is closely followed by Satellite Internet and DSL. The upload speed are typically limited to 128 Kbps.
Mobile hotspot: As the name implies, Mobile hotspot connections can be used to provide Internet access for multiple users in a mobile environment. These days, normal smart phones are offering mobile hotspot capability via the carrier Internet access. A device with just wireless LAN access can connect to the mobile hotspot (it can be smart phone, tablet PC or a desktop computer with wireless LAN) and access the Internet. Mobile hotspot is also known as MiFi.
Note: MiFi is a brand name used to describe a wireless router that acts as mobile Wi-Fi hotspot
Hotspot/tethering:A smartphone and a compatible USB cable is all that you need to connect your cellular internet connection to your laptop or tablet in a process called tethering. You may also connect your desktop computer by tethering via your smart phone using WiFi connection. In this process the Internet connection is used to create a mobile hotspot, through which the other devices can access resources on the internet. Tethering, or phone-as-modem (PAM), is the sharing of a mobile device's internet connection with other wirelessly connected computers.
Network architecture devices:
Hub: A hub is basically a multi-port repeater. When it receives a packet, it repeats that packet out each port. This means that all computers that are connected to the hub receive the packet whether it is intended for them or not. It's then up to the computer to ignore the packet if it's not addressed to it. This might not seem like a big deal, but imagine transferring a 50 MB file across a hub. Every computer connected to the hub gets sent that entire file (in essence) and has to ignore it.
Bridge: A bridge is a kind of repeater, but it has some intelligence. It learns the layer 2 (MAC) addresses of devices connected to it. This means that the bridge is smart enough to know when to forward packets across to the segments that it connects. Bridges can be used to reduce the size of a collision domain or to connect networks of differing media/topologies, such as connecting an Ethernet network to a Token Ring network.
Switch: A switch is essentially a multi-port bridge. The switch learns the MAC addresses of each computer connected to each of its ports. So, when a switch receives a packet, it only forwards the packet out the port that is connected to the destination MAC address. Remember that a hub sends the packet out every port, and you can see how much more efficient this it
Networking tools:
A toner probe is an electronic test instrument to help trace wires. One part (the tone generator) induces a tone on a pair of wires, and with the other you part (the tone probe) you can detect the tone at the other end to trace where the wires go. You can trace wires through walls using a tone probe, and determine which pair is carrying the signal you induced at the other end. Toner probes are used to locate the correct cable coming into a patch panel from the wall outlet when connections have either not been labelled or the labels have been removed from the patch panel. They are two-piece units (sometimes called Fox and Hound) where one end sends a signal and the other end is used to locate the wires that contain the signal in the switch room.
A cable tester is used to verify that all of the intended connections exist and that there are no unintended connections in the cable being tested. When an intended connection is missing it is said to be "open". When an unintended connection exists it is said to be a "short" (as in short circuit). If a connection "goes to the wrong place" it is said to be "miswired" (the connection has two faults: it is open to the correct contact and shorted to an incorrect contact).
The main difference between a cable tester and a toner probe is that in the former, you have access to the both ends of the cable at the same time, and you normally to Open or Short testing (to determine right pins are connected), and in the latter, you dont have simultaneous physical access to both ends of the cable.
Punch-down tool : is used when you are securing cables to the patch panel that have been run from the wall outlets into the switch room. A wire is pre-positioned into a slotted post, and then the punch-down tool is pressed down on top of the wire, over the post. Once the required pressure is reached, the internal spring is triggered, and the blade pushes the wire into the slot, cutting the insulation and securing the wire.
Crimper : is used to attach a connector to a cable by securing each wire (8 of them in a twisted-pair wire) to the proper connector in an RJ-45 connector. It usually also includes a stripper as well.
Loopback plugs: are used to test the functionality of various types of ports, but their most common use is to test a network card. These plugs send a signal out of the card and then loop it back into the same card to test its operation. They look like an RJ-45 connector without the cable.
Parallel loop back tester : will provide you with the ability to diagnose any problems with your DB25 parallel port or DB25 parallel cable. This loop back tester consists of a single DB25 male end for verifying accurate DB25 port functioning.
WI-FI networking standards:
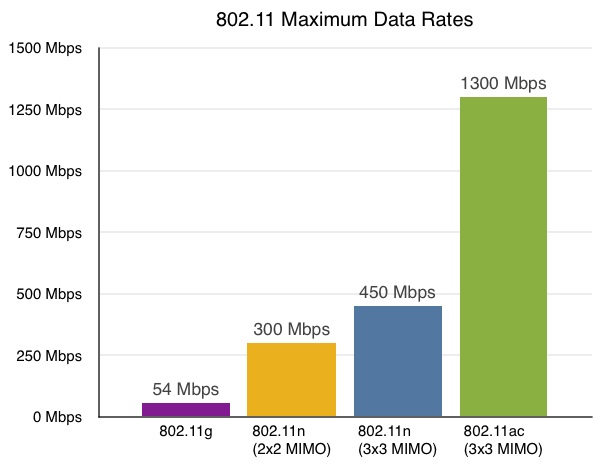
802.11ac is called Gigabit Wi-Fi or 5G Wi-Fi.. 802.11ac is a 5-GHz only technology that can use wider channels in the 5-GHz band, more spatial streams, and multi-user MIMO (MU-MIMO).
Encryption types are used to provide security for wireless transmissions. The three widely used wireless encryption types are Wired Equivalent Privacy (WEP), Wi-Fi Protected Access (WPA), and WPA2.
Attackers can easily discover the security key used for a WEP encrypted network. Because of this, WEP is not recommended for use. WPA was created as an interim replacement for WEP. Later, WPA2 was standardized and is now recommended for use whenever possible. WEP, WPA, and WPA2 commonly use a passphrase or a pre-shared key. When joining a network, you need to know the name of the network, the type of security used, and the passphrase.
WPA and WPA2 both can use either Advanced Encryption Standard (AES) or Temporal Key Integrity Protocol (TKIP) to encrypt the data. AES is a widely used standard and recommended for use.
WEP is the least secure wireless encryption type, and WPA2 is the most secure wireless encryption type. WPA2 with AES provides strong security for wireless networks.
Wired Equivalent Privacy (WEP), Wi-Fi Protected Access (WPA), and Wi-Fi Protected Access II (WPA2) are the primary security algorithms. WEP is the oldest and has proven to be vulnerable as more and more security flaws have been discovered. WPA improved security, but is now also considered vulnerable to intrusion. WPA2, while not perfect, is currently the most secure choice. Temporal Key Integrity Protocol (TKIP) and Advanced Encryption Standard (AES) are the two different types of encryption used on networks secured with WPA2.
TKIP and AES are two different types of encryption that can be used by a Wi-Fi network. TKIP is actually an older encryption protocol introduced with WPA to replace the very-insecure WEP encryption at the time. TKIP is no longer considered secure, and is now deprecated. AES is a more secure encryption protocol introduced with WPA2.
An SSID is a 32-character (maximum) alphanumeric key identifying the name of the wireless local area network. Some vendors refer to the SSID as the network name. For the wireless devices in a network to communicate with each other, all devices must be configured with the same SSID.
Disabling SSID broadcast is just one of many possible techniques for tightening security on a Wi-Fi network.
WiFi is a local area wireless computer networking technology that allows electronic devices to connect to the network
WiFi Analyzer can help you to identify Wi-Fi problems, find the best channel or the best place for your router/access-point.
WEP, short for Wireless Equivalent Protection, is a security protocol designed to provide protection equivalent to wired LANs. WPA is an improved security protocol compared to WEP.
WEP was introduced in the wireless networks to provide same level of protection as that of wired networks. However, it has been found to be easily broken, and later replaced by WPA and WPA2.
The Wireless function key typically turns on/off the wireless radio. If you inadvertently press the function key, it is possible that you are not able to access the Internet, if using WiFi
A DMZ (De Militarized Zone) is an area on your network that allows public access while only allowing limited access to your internal network. Typically, you put your web server, gaming server, or mail server on DMZ to allow public access.
802.11 standards
802.11a standard provides wireless LAN bandwidth of up to 54Mbps in the 5GHz frequency spectrum. The 802.11a standard also uses orthogonal frequency division multiplexing (OFDM) for encoding rather than FHSS or DSSS.802.11a is not compatible. Bluetooth is entirely a different protocol standard.
802.11b standard provides for bandwidths of up to 11 Mbps (with fallback rates of 5.5, 2, and 1 Mbps) in the 2.4G Hz frequency spectrum. This standard is also called Wi-Fi or 802.11 high rates. The 802.11b standard uses only DSSS for data encoding.802.11b is compatible with 802.11g
802.11g standard provides for bandwidths of 20 Mbps+ in the 2.4 GHz frequency spectrum. This offers a maximum rate of 54 Mbps and is backward compatible with 802.11b.
802.11n the newest of the wireless standards you need to know for the exam is 802.11n. The goal of the 802.11n standard is to significantly increase throughput in both the 2.4 GHz and the 5 GHz frequency range. The baseline goal of the standard was to reach speeds of 100 Mbps, but given the right conditions, it is estimated that the 802.11n speeds might be able to reach 600 Mbps. In practical operation, 802.11n speeds will be much slower.
Bluetooth Class 3 supports speeds up to 1m at 2.4GHz (1mW power output max)
Bluetooth Class 2 supports speeds up to 10m at 2.4GHz (2.5mW power output max)
Bluetooth Class 1 supports speeds up to 100m at 2.4GHz (100mW power output max)
All the short range wireless technologies fall under PAN viz. Bluetooth, Zigbee, Zwave, Infrared etc. It is mainly designed and developed for low data rate monitoring and control applications. PAN wireless technologies have become very popular in IoT (Internet of things) networks.
Bluetooth conforms to its own standards, and not compatible with 802.11 standards.
Bluetooth: is a wireless protocol for exchanging data over short distances from fixed and mobile devices, creating personal area networks. Most mobile devices are Class 2, providing a range of up to 10 m. Class 1 devices have a range of up to 100 feet.
Typical 802.11 data rates are shown in the figure below:
WINS and DNS are both name resolution services for TCP/IP networks. While WINS resolves names in the NetBIOS name space, DNS resolves names in the DNS domain name space. WINS primarily supports clients that run older versions of Windows and applications that use NetBIOS. Windows 2000, Windows XP, and Windows Server 2003 use DNS names in addition to NetBIOS names. Environments that include some computers that use NetBIOS names and other computers that use domain names must include both WINS servers and DNS servers.
MIMO (Multi Input Multi Output) wireless technology is able to considerably increase the capacity of a given channel . By increasing the number of receive and transmit antennas it is possible to linearly increase the throughput of the channel with every pair of antennas added to the system. As spectral bandwidth is becoming very expensive, techniques are needed to use the available bandwidth more effectively. MIMO wireless technology is one of these techniques. Note that by using 4 antennas (4X4 MIMO), it is possible to increase the signal bandwidth, say in 802.11n by another 150Mbps to a total of 600Mbps.
NAT - Short for Network Address Translation is used to map internal IP addresses to external IP addresses. Typically, a router or a Firewall is used for this purpose.
NAT is basically a translation from one network address, to another one.
Static NAT - means that the address ALWAYS translates to the same address, every single time
Dynamic NAT - means that the address may translate to one of several addresses, it doesn't necessarily have a one-to-one correspondence, like the static NAT. dynamic NAT is used with a pool of addresses that addresses could be translated to
PAT - means that the translation is to a address/port combination, such that one address can "overload" the NAT.that is, one address can translate to 10.10.10.1:50000 and another address can translate to 10.10.10.1:40000, for example.
The form of NAT most familiar to you would probably be PAT, as your home internet connection uses a PAT so that multiple devices inside your home network connect out through a single global address. Each of your internal devices translates to a different address/port combination.
Universal Plug and Play (UPnP) is a standard that uses Internet and Web protocols to enable devices such as PCs, peripherals, intelligent appliances, and wireless devices to be plugged into a network and automatically know about each other. With UPnP, when a user plugs a device into the network, the device will configure itself, acquire a TCP/IP address, and use a discovery protocol based on the Internet's Hypertext Transfer Protocol ( HTTP ) to announce its presence on the network to other devices. For instance, if you had a camera and a printer connected to the network and needed to print out a photograph, you could press a button on the camera and have the camera send a "discover" request asking if there were any printers on the network. The printer would identify itself and send its location in the form of a universal resource locator ( URL ).
The camera and printer would use Extensible Markup Language ( XML ) to establish a common language, or "protocol negotiation", to talk to each other and determine capabilities. Once a common language was established, the camera would control the printer and print the photograph you selected.
Port forwarding : can be used to provide access to a system within a private network from the Internet. For example, all traffic coming in port 80 can be forwarded to a web server on an internal network. Port forwarding sends traffic coming in from the Internet on a specific port to an internal system with a specific IP address.
Port triggering : uses one outgoing port as a trigger to open a specific incoming port. For example, an application might send traffic out on port 3356 and receive traffic in on port 5668. A port trigger on the router or firewall will automatically open incoming port 5668 only when traffic is sensed going out of port 3356. Port triggering opens a specific incoming port only after traffic is sent out on a specific port.